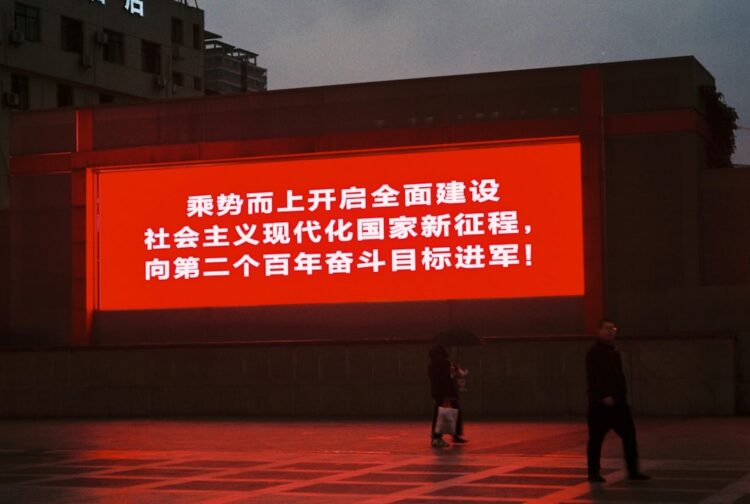
A massive data breach at Chinese cybersecurity firm Knownsec has exposed the digital machinery behind Beijing’s global cyber espionage network, in what security experts are calling one of the most consequential leaks in the history of state-backed hacking.
More than 12,000 confidential documents, which were originally uploaded to GitHub before they were removed for violating the platform’s terms of service, have revealed the scope, sophistication, and international reach of China’s cyber operations, providing an unprecedented window into how its intelligence ecosystem functions.
Founded in 2007 and backed by tech giant Tencent, Knownsec has long operated at the nexus of China’s commercial cybersecurity sector and its state-directed intelligence apparatus. The company’s clients reportedly include government departments, financial institutions, and critical infrastructure operators, placing it squarely within Beijing’s digital command chain. That connection is now under renewed scrutiny following the leak, which has laid bare a sprawling cyber arsenal designed to infiltrate, monitor, and manipulate targets worldwide.
The trove details an extensive suite of offensive tools and data theft campaigns. Researchers analysing the leaked files say they include Remote Access Trojans (RATs) built for every major operating system (Windows, macOS, Linux, iOS, and Android), underscoring China’s capability to breach nearly any endpoint on the planet.
Other components include Android-based surveillance modules capable of extracting chat histories, contacts, and location data from popular messaging platforms.
Among the most alarming revelations are hardware-based exploits attributed to Knownsec’s engineering teams, including a compromised portable power bank designed to covertly siphon data from any connected device. Such hardware-level compromise points to an advanced supply-chain strategy, where seemingly benign consumer or enterprise products become tools of persistent espionage.
Data exfiltration appears to have been central to Knownsec’s operations. Internal spreadsheets list vast stolen datasets: 95GB of Indian immigration records, 3TB of South Korean telecom data, and 459GB of Taiwanese road planning files, alongside material from more than 20 other nations including the United Kingdom, Japan, and Nigeria.
Beijing’s official response has been characteristically opaque. When asked about the breach, the Chinese Foreign Ministry neither confirmed nor denied the incident, instead repeating its standard line opposing “all forms of cyberattacks.”
For Western intelligence and defence agencies, the fallout is already significant. The leak’s technical breadth – spanning mobile, hardware, and cloud environments – has made it a rare and valuable intelligence asset for defenders, but also a sobering reminder of how extensively state-aligned firms have embedded offensive capabilities into the global digital fabric.
“The Knownsec breach doesn’t just reveal tooling, it reveals doctrine,” said Richard Blech, founder and CEO of XSOC CORP. “The leaked ecosystem points to a unified strategy: collect at scale, correlate across domains, and train AI systems to infer what encryption still leaks. When you combine massive exfiltration of immigration, telecom, mobility [and] infrastructure data with state-aligned contractors like Knownsec and I-Soon [which itself was the subject of a leak in 2024], the goal becomes clear: build adversarial models that reconstruct behaviour and intent from encrypted telemetry, timing patterns, and metadata, not plaintext. That is the core of AI-driven Data Attacks (AIDA).”
Blech added that this represents a fundamental shift in cyber doctrine.
“The world still fixates on decryption, yet this leak shows China’s pivot toward observation and inference, where packet cadence, protocol signatures, cross-dataset mapping, and device-level access feed models optimized to predict, not break. This is the Cognitive War: a shift from hacking systems to training models that understand systems, even when the data itself is encrypted.”
For the defence sector, the Knownsec breach underscores how military, aerospace, and dual-use technology suppliers remain prime targets – not only for direct intrusion, but as data sources feeding the kind of AI systems Blech describes.
These models don’t simply catalogue stolen information; they analyse traffic patterns, operational rhythms, and communication signatures to anticipate how adversaries think and act.
Quantum-safe encryption offers one path to resilience, particularly as quantum computing threatens to dismantle existing cryptographic standards. Yet as the Knownsec case illustrates, even unbroken encryption can leak information through its metadata. AI tools, meanwhile, can digest and correlate this vast data haul far faster than any human analyst, giving state actors new predictive capabilities that sit beneath traditional detection thresholds.