China has formally accused US intelligence agencies of exploiting a previously unknown Microsoft Exchange zero‑day vulnerability to orchestrate a prolonged cyberattack against its defence sector.
China’s National Internet Emergency Response Center (CNCERT), which describes itself as a non-governmental cybersecurity technical center, alleges that US intelligence hackers leveraged the flaw in Microsoft’s Exchange software to breach and maintain control of the email server of a major Chinese military-related enterprise (which it did not name) between July 2022 and July 2023.
During this alleged cyber‑espionage campaign, CNCERT claims the perpetrators stole sensitive defence data and maintained persistent access throughout that period.
“The attacker … launched more than 40 network attacks, stealing the emails of 11 people, including the senior management of the enterprise, involving the relevant design schemes, system core parameters and other contents of our military industry products,” reads a version of CNCERT’s statement translated by Resilience Media.
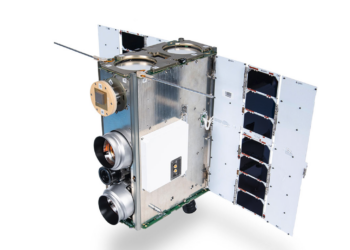
CNCERT claimed that, in a separate instance, US agents exploited vulnerabilities in an electronic file system, unrelated to Microsoft Exchange, to conduct cyberattacks against another Chinese military enterprise operating in the communications and satellite internet sector between July and November 2024, also exfiltrating confidential information.
“The attacker used the enterprise’s system software upgrade service to deliver theft Trojan horses to the enterprise’s intranet, invaded and controlled more than 300 devices, and searched for keywords such as ‘military special network’ and ‘core network’ to steal sensitive data on the accused host,” reads CNCERT’s alert.
Guo Jiakun, spokesperson of the Ministry of Foreign Affairs of China, said in a statement that the “US used its allies in Europe and in China’s neighboring region … to launch the cyberattacks.” He added that CNCERT’s alleged findings are “the latest evidence of the US government’s malicious cyberattacks on China” and “once again shows that the US is the top cyber threat faced by China.”
In a 1 August alert, CNCERT added that these alleged attacks, which it claims have been aggressively carried out since the US National Security Agency (NSA)’s alleged cyberattack on China’s Northwestern Polytechnical University in 2022, pose “a serious threat to the scientific research and production security of China’s defense and defense industries, and even to national security.”
Neither Microsoft nor the NSA immediately responded to Resilience Media’s questions.
These accusations follow a broader pattern of mutual cyberespionage allegations between Beijing and Washington. China’s latest claims echo earlier US assertions that Chinese state‑sponsored hackers have targeted its systems.
Notably, in 2021, Microsoft revealed that China-linked threat group Hafnium, also known as Silk Typhoon, had exploited multiple zero‑day vulnerabilities in Exchange to launch widespread intrusions across the globe. Those attacks affected tens of thousands of servers, including those belonging to US defense contractors, law firms, universities, NGOs, and healthcare research institutions. In response, Microsoft and international authorities issued patches and warnings to mitigate the damage.
Just last month, Microsoft said China-backed hacking groups had also exploited flaws in SharePoint to target governments and businesses that use the file-sharing software.
The UK’s National Cyber Security Centre told the BBC that these attacks, which focused on stealing intellectual property from organisations related to defense and strategic planning, targeted “a limited number” of SharePoint Server customers in the UK.
CNCERT’s latest allegations represent a rare reversal of narrative: China is now asserting that the US deployed analogous tactics against Chinese military‑industrial targets, underscoring intensifying tensions in cyberspace between the world’s two largest economies.
China’s accusations come just weeks after Ukraine’s national cyber authority warned that Russian state-backed hackers had been using AI-powered malware in active attacks targeting the country’s defence and security sector.