CERT Polska has described December’s cyberattack on Poland’s energy sector as an act of “digital arson.” A report from the government group, which provides emergency response to IT-related incidents, reveals that — contrary to earlier reports that attributed the cyberattack to sophisticated zero-day exploits — attackers gained access through a much more straightforward route: exposed firewalls with no multi-factor authentication.
The report offers the clearest technical account yet of what happened on 29 December, when multiple energy and industrial sites across Poland were hit in a coordinated campaign that prioritised destruction over disruption.
At least 30 wind and solar installations were affected, along with a large combined heat and power plant that supplies heat to hundreds of thousands of homes and a manufacturing company.
While electricity generation continued, operators temporarily lost remote visibility and control at several sites after attackers deliberately severed communications and damaged operational systems.
According to CERT Polska, the attackers didn’t weaponise a zero-day or exploit a supply chain; they walked in through internet-facing firewalls and VPNs that lacked multi-factor authentication and, in some cases, weak or reused passwords.
That access was sufficient to move laterally into internal systems and onward to operational technology that should never have been reachable from the public internet.
CERT Polska says the attackers moved quickly from access to damage, attempting to corrupt firmware, delete data, and disable remote terminal units responsible for monitoring and control. There was no indication of espionage or data theft, only deliberate destruction.
An analysis published by industrial cybersecurity firm Dragos provides additional context on the incident, particularly regarding the selection of targets.
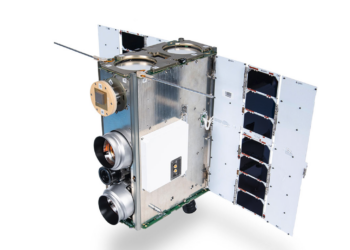
Dragos researchers described the operation as “the first major cyberattack targeting distributed energy resources,” warning that wind farms, solar installations, and other decentralised assets present a growing and under-secured attack surface. Unlike traditional power plants, these sites are often designed for remote management at scale, using standardised hardware and configurations that make them efficient to run but easier to compromise en masse.
That assessment helps explain the attackers’ apparent focus. According to Dragos, once the adversary worked out how to access one site, the same approach could be replicated across many others using similar equipment. The result was a broad, coordinated impact that did not bring down the national grid but knocked out monitoring and control at dozens of locations simultaneously. Some equipment was damaged severely enough to require manual intervention and replacement, resulting in a longer recovery effort.
On attribution, CERT Polska diverges from some earlier assessments.
While ESET and Dragos linked the attacks to Sandworm, the Russia-backed group notorious for physically destructive attacks, CERT Polska’s analysis of the attack infrastructure found a high degree of overlap with activity publicly tracked under names such as “Berserk Bear” and “Dragonfly”, two other Russia-backed groups. It describes this as the first publicly documented case of destructive activity attributed to that group, which is better known for traditional cyberespionage.
Perhaps the most uncomfortable takeaway from the CERT Polska report is how preventable much of the intrusion appears to have been. The attack didn’t succeed because of sophisticated tradecraft, but because basic safeguards were missing. Multi-factor authentication, proper segmentation, and stricter controls on exposed devices would have significantly complicated operations, rather than leaving critical systems easy to reach.
We have reached out to industry sources for reaction and will update this post as we learn more.